PSA: If you or someone you know uses the Contact Form 7 Datepicker plugin for your WordPress blog or website, you need to deactivate or remove it immediately!
The Threat Intelligence team over at Wordfence were the ones who discovered a stored XSS (Cross Site Scripting) vulnerability in the Contact Form 7 Datepicker plugin. Here’s some technical details regarding the vulnerability:
Description: Authenticated Stored Cross-Site Scripting(XSS)
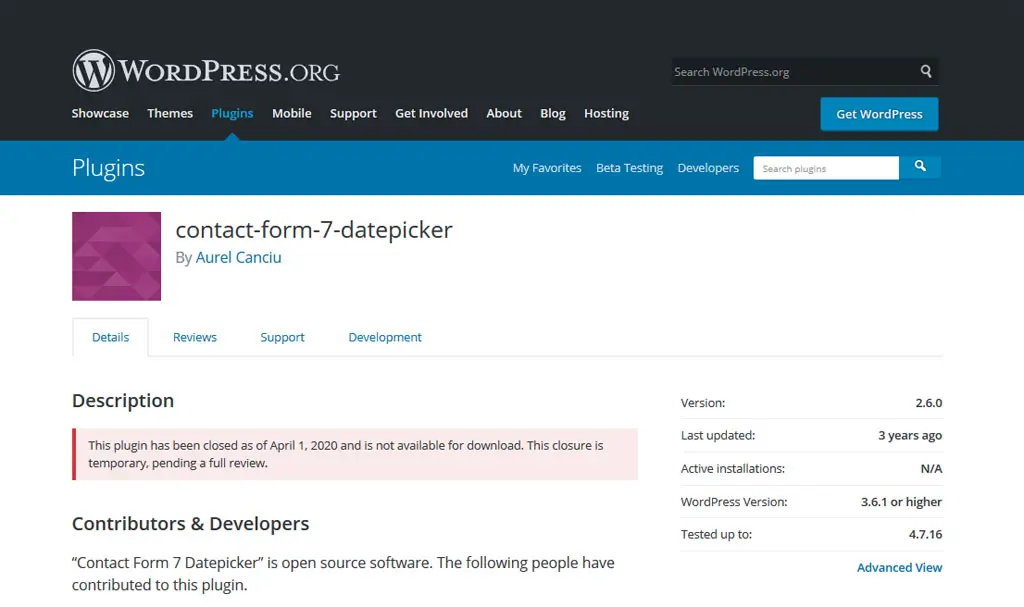
Affected Plugin: Contact Form 7 Datepicker
Plugin Slug: contact-form-7-datepicker
Affected Versions: <= 2.6.0
CVE ID: Will be updated once identifier is supplied
CVSS Score: 7.4(High)
CVSS Vector: CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:L
Fully Patched Version: N/A
This plugin has been installed over 100,000 sites, which is quite a lot. I’ve never used this plugin before but based on the number of installations, it’s safe to say that it is quite popular. Unfortunately, the plugin authors have long neglected it and haven’t maintained the plugin for quite a while. That, I believe is one of the reasons why this vulnerability existed. Malicious users and hackers are always on the lookout for vulnerable plugins such as this.
The folks at Wordfence has notified the plugin authors as well as the WordPress plugin team regarding this issue. Because of that, the Contact Form 7 Datepicker Plugin is now officially removed from the WordPress Plugins Repository.
Kudos to the Wordfence team for alerting the WordPress plugin team as well as the entire community regarding this issue.
For all WordPress users out there. If you’re not yet in the habit of constantly updating your WordPress installation, plugins, and themes, please start doing it now. I’m telling you, doing this will save you from a lot of future headaches or problems. Better safe than sorry!